IP Access Rules
Last update:2026-05-15 10:32:54
On the Internet, IP addresses are unique and remain the same throughout a request. When a client initiates a request to CDN edge servers, the CDN edge servers can obtain the client’s IP address. Therefore, IP addresses can be utilized for access control. Upon receiving a request from a client, the CDN node checks the client’s IP address and then either allows or denies user requests that comply with specific rules.
The IP access rule is suitable for the following scenarios:
- When abnormal access behavior is detected from certain IP addresses, such as hotlinking or certain attacks, these IP addresses can be added to the blocklist. Consequently, access attempts from these IP addresses to CDN nodes will be directly denied.
- When access to accelerated content is restricted based on IP addresses, such as only allowing access to employees within an organization and denying access to individuals outside the organization, the fixed office public IP addresses of the organization can be added to the allowlist. Consequently, access attempts from IP addresses other than those on the allowlist will be directly denied.
- When access to content is restricted based on geographic regions, such as allowing viewing or downloading only for users in the New York area and denying access to users from other regions, the region access permission feature can be used.
How to Set Up the IP Access Rule
- Log in to the CDNetworks Console and select the appropriate product.
- Go to the Configuration, locate the domain you wish to configure, and click Edit Configuration
 .
. - Navigate to Access Control - IP Access List in the left sidebar and click Add.
- Configure the settings as follows based on your needs.
Apply to
This defines the scope for the requests that the rule will apply to. You can choose from the following options:
| Setting | Description |
|---|---|
| All Requests | The access control rule applies to all types of requests. |
| Only Homepage | Applies only to the root directory of the domain, such as http://domain/ or https://domain/. |
| Specific File Type | Applies only to specific types of files. You can select from the predefined file types on the left or define custom file types. Separate multiple custom types with a semicolon ; (e.g., jpg;png). |
| Specific URL Path | Applies only to requests for content at a specific URL path. Two URL path matching options are available:Full URL Path: Complete URL path, including parameters (e.g., path/index.html?abc=123). Ignore Query String: URL path without query parameters (e.g., path/index.html). |
| Specific Directory | Applies to requests under specific directories. For example, /file/abc/ applies to all content under http://domain/file/abc/*.Note: Directories must start and end with /, and can only contain letters, numbers, and certain special characters (underscore, hyphen, percent sign, dot). Multiple directories are supposed to be separated with line breaks. |
| URL Pattern (Regex) | Uses regular expressions to control the scope for the requests that the rules will be applied to. For example, the pattern *.jpg$ ensures that access control applies to all URLs ending with .jpg. |
Advanced Scope Conditions
You can further refine the rule’s scope using Advanced Scope Conditions. This will intersect with the basic Apply to for precise control. Select one or more parameters to form an AND relationship with the basic rules to target specific requests or responses.
| Parameter | Description |
|---|---|
| Region or Exclude Regions | Supports direct search selection from the list of countries/regions provided by CDNetworks; For Mainland China, it is possible to select specific provinces or larger geographical areas, such as East Region and Southwest Region. |
| Exclude File Type | Excludes certain file types. Separate multiple types with ;. |
| Exclude Custom File Type | Excludes custom file types as needed. Separate multiple types with ;. |
| Exclude Directory | Excludes specific directory paths. Paths must start and end with /. Separate multiple directories with ;. |
| Exception URL (Regex) | Excludes URLs using regex, e.g., .*\.jpg$. |
| Access-Control-Allow Methods | Matches HTTP request methods. Separate multiple methods with ;, e.g., GET;POST. |
| Exclude Request Method | Excludes specific HTTP request methods. |
Rule Type
You can set up either an IP Blocklist or an IP Allowlist:
| Type | Description |
|---|---|
| Blocklist | Set an IP blocklist to deny access from certain IPs or IP ranges. We provide four options:Custom: Define your IP blocklist by adding specified IP addresses and ranges. Access from these IPs will be denied.All IPs: Access denied for all IP addresses.All IPv4: Access denied for IPv4 addresses only.All IPv6: Access denied for IPv6 addresses only.You can add exceptions to permit access from certain IPs within a blocked range by Set IP and CIDR Block Exceptions. Multiple exceptions can be added simultaneously and should be separated by ;. |
| Allowlist | Set an IP allowlist to allow access only from specific IPs or IP ranges. Multiple IPs or ranges can be added simultaneously and should be separated by ;. |
The system supports only one allowlist rule. If multiple IPs or IP ranges are needed, they must all be included within this single allowlist.
Action
When a client’s IP does not meet the set rules, and their request is denied by the CDN, choose whether to return an error code directly or redirect to another URL:
- Block Access: The CDN rejects the request with a
403error. - Redirect: The CDN redirects the requests to another URL.
Case-Insensitive Match
The default for this setting is Yes.
- The Yes option indicates that the Apply to will be case-insensitive. Two requests with URLs that differ only in case will both match the rule you set. For example, if you configure
/domain/a.jpgfor Specific URL Path, both requests for/domain/a.jpgand/domain/A.jpgwill be matched. - Conversely, if you choose No, case differences with settings in Apply to will not be ignored in incoming requests, and only requests matching the case exactly as specified in the Apply to will follow the IP access rules.
Priority
When multiple access control rules are configured, the CDN prioritizes them based on their numerical value, executing higher numbers first.
After you have completed setting the configurations, please click OK and then select Next to submit your settings. To minimize any potential disruptions to your production environment, we strongly recommend conducting a Pre-deploy test in a staging environment. This crucial step ensures that your configurations are accurate before they go live. Once you have verified the accuracy of the settings, click Deploy Now to implement them in the live environment. The configurations typically become effective within 3-5 minutes. For comprehensive guidance on pre-deployment testing and to verify the effectiveness of your configurations, please consult the tutorial Deploy the Configurations to Staging Environment for Validation.
Best Practices
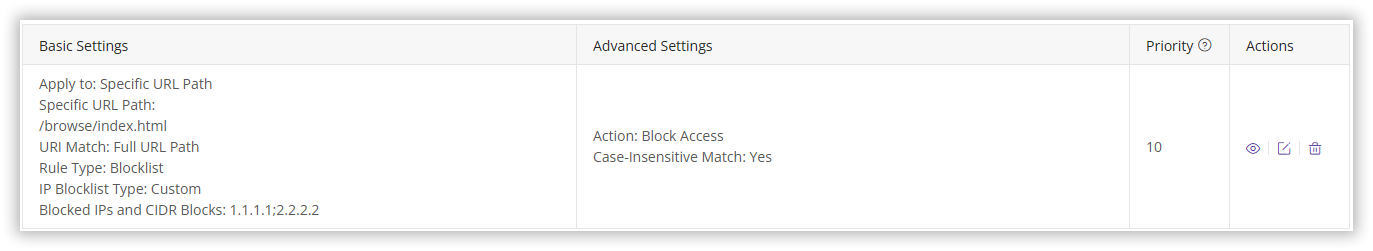
Example 1: Configure an IP blocklist
Prohibit access from IP addresses 1.1.1.1 and 2.2.2.2 to http://cdnetworks.com/browse/index.html.
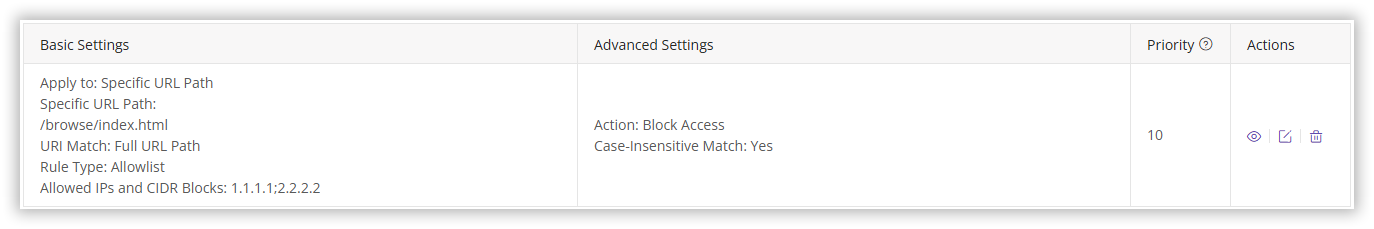
Example 2: Configure an IP Allowlist
Allow access only from IP addresses 1.1.1.1 or 2.2.2.2 to http://cdnetworks.com/browse/index.html.
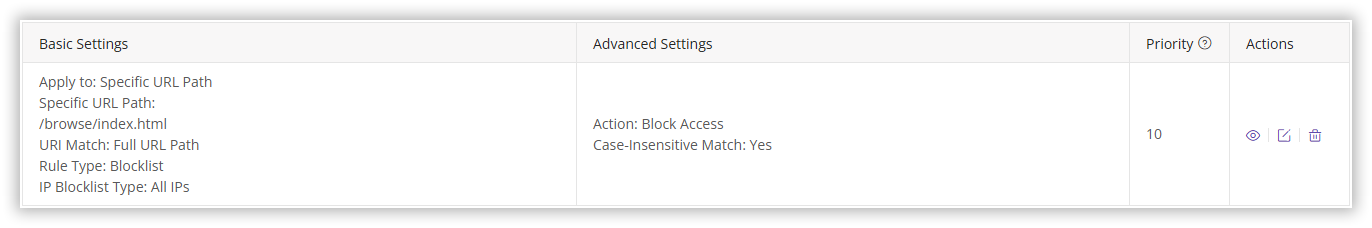
Example 3: Permanent URL Ban
Block access to http://cdnetworks.com/browse/index.html for all users. The block will remain until the configuration is manually removed.
Notes
Please DO NOT configure both IP Blocklists and Allowlists simultaneously, as this may result in access to CDN being denied, potentially impacting your business. For example, configuring both an IP blocklist and allowlist as shown below can lead to all accesses being denied by the CDN.
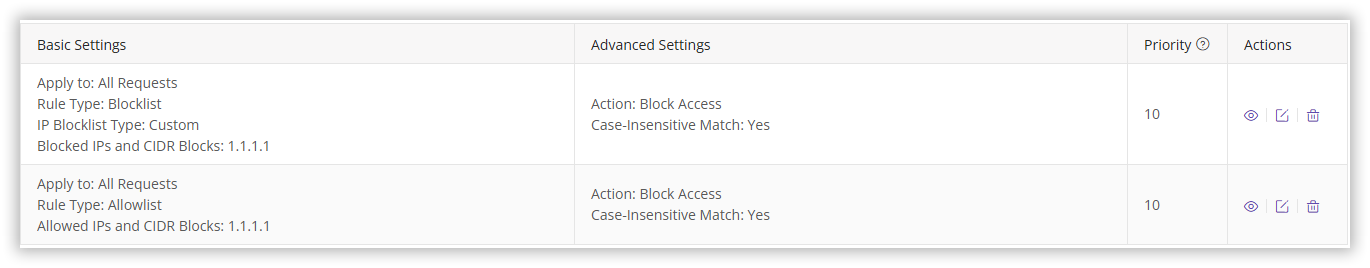
Why would all requests be denied?
- When a request comes from IP
1.1.1.1, it matches the IP blocklist rules and is denied by the CDN. - Requests from other IPs, while not denied by the blocklist, fail to meet the allowlist rule (which only allows access from
1.1.1.1) and are also denied.
If you need to configure both a blocklist and an allowlist, please contact our technical support for assistance to ensure proper setup.