Device List
Last update:2023-06-19 17:00:34
1. Usage Scenario
This page gives an overview and device management capability of all devices that have accessed ESA, including authorized devices, unauthorized devices and blocklist.
2. Operation Steps
1) All Devices
Go to Device Security–>Device List–> All Devices, you will see all the devices that have accessed to ESA.
Note that for the devices that have been imported on Authorized by Device List but have not yet login to ESA are not listed.
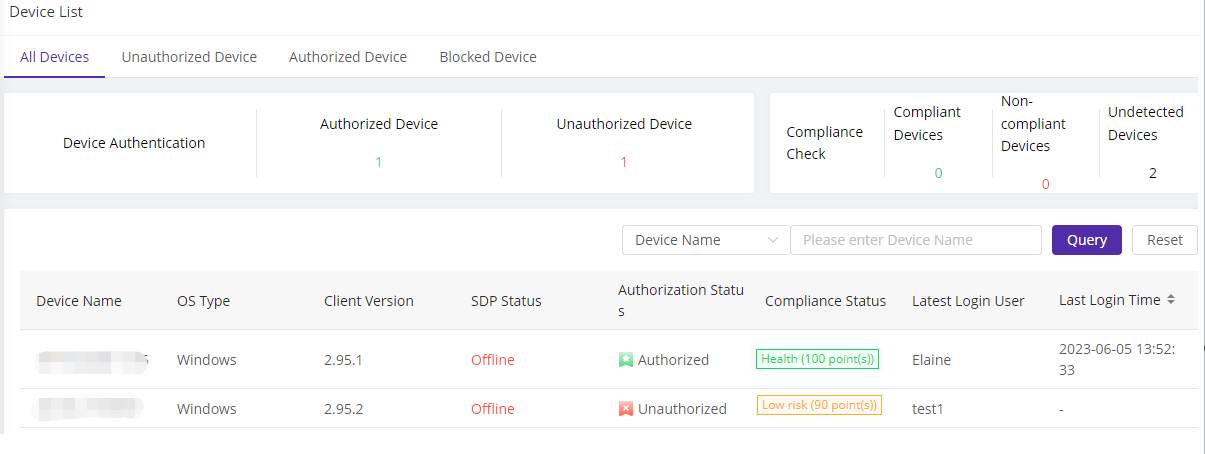
You will see the parameters including:
| Field Name | Explanation |
|---|---|
| Device Name | The login device name |
| OS Type | The operating system of the device that access to ESA, supported OS: Windows, macOS, Android, iOS, Linux, Ubuntu, etc. |
| Client Version | The ESA client version on the device |
| SDP Status | Indicates whether the device has been connected to security gateway |
| Authorization Status | Indicates whether the device is an authorized device |
| Compliance Status | After administrator enable the compliance check policy, when user login to ESA, the device will be checked according to the policy. This parameter displays the check result and risk level. Compliance check is available on Premium bundle |
| Last Login User | The last user account that has login to ESA on the device |
| Last Login Time | The last time when user login to ESA on the device |
2) Unauthorized Device
Go to Device Security–>Device List–> Unauthorized Device, you will see all the devices that have accessed to ESA that are not authorized yet.
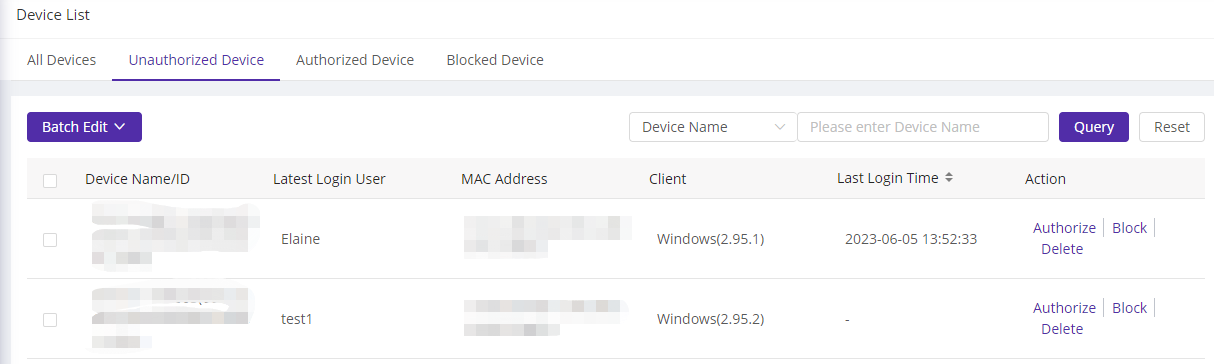
You will see the parameters including:
| Field Name | Explanation |
|---|---|
| Device Name/ID | The login device name and ID. The device ID is a unique ID assigned to this device by ESA platform |
| Last Login User | The last user account that has login to ESA on the device |
| MAC Address | The MAC address of the login device, including the address of wired network card, wireless network card and MAC address |
| Client Version | The operating system and ESA client version on the device |
| Last Login Time | The last time when user login to ESA on the device. |
| Action | From list, administrator can do Authorize, Block and Delete operation to the device. Authorize: the device will be authorized and add to Authorized Device list Block: the device will be added to blocklist, the user account will logout and unable to login Delete: delete the device from list, but user can login next time |
3) Authorized Device
Go to Device Security–>Device List–> Unauthorized Device, you will see all the authorized devices that have accessed to ESA.
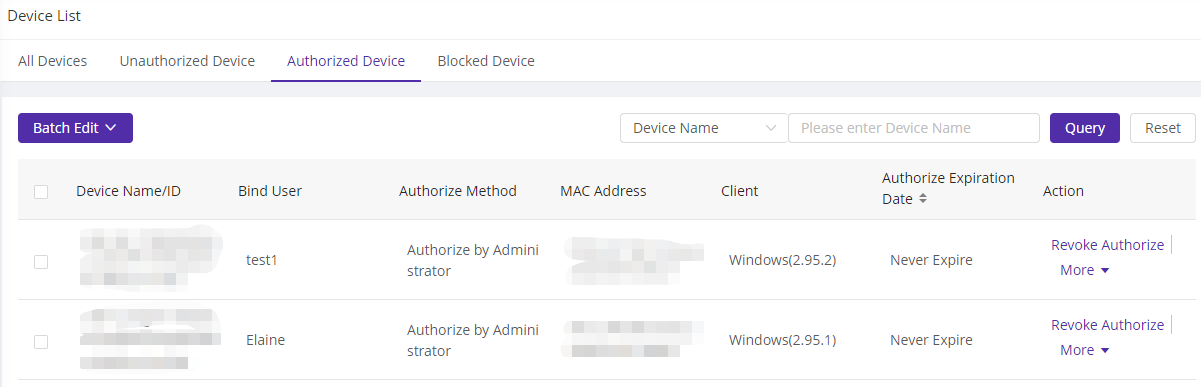
You will see the parameters including:
| Field Name | Explanation |
|---|---|
| Device Name/ID | The login device name and ID. The device ID is a unique ID assigned to this device by ESA platform |
| Bind User | The user that has been bound to this device. Each device can only be bound to one user. |
| Authorize Method | Indicates how the device was authorized, by device list, by user or by administrator |
| MAC address | The MAC address of the login device, including the address of wired network card, wireless network card and MAC address |
| Client Version | The operating system and ESA client version on the device |
| Authorize Expiration Date | Indicates the expire date of authorization status |
| Action | From list, administrator can do Revoke Authorize, Block and Adjust authorize expire date operation to the device. Revoke Authorize: revoke the authorization from the device and move it to unauthorized device list Block: the device will be added to blocklist, the user account will logout and unable to login Adjust authorize expire date: change the expire date of authorization to the device |
4)Blocked Device
Go to Device Security–>Device List–> Blocked Device, you will see all the devices that have accessed to ESA but already been added to blocklist.
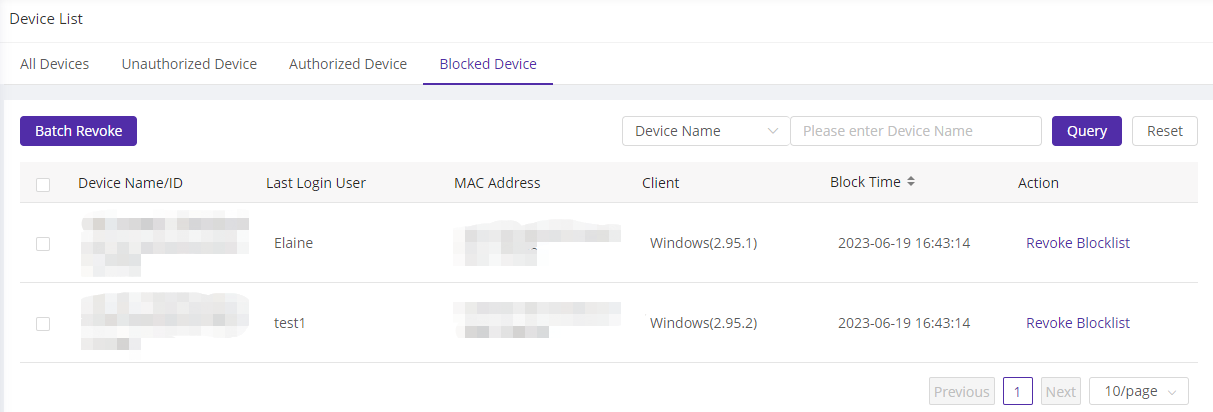
You will see the parameters including:
| Field Name | Explanation |
|---|---|
| Device Name/ID | The login device name and ID. The device ID is a unique ID assigned to this device by ESA platform |
| Last Login User | The last user account that has login to ESA on the device |
| MAC address | The MAC address of the login device, including the address of wired network card, wireless network card and MAC address |
| Client Version | The operating system and ESA client version on the device |
| Block Time | The time when the device was added to blocklist |
| Action | Administrator can revoke the device from blocklist. Once revoked, the device will be moved to Unauthorized Device list. |