About Alert Management
最終更新日:2026-03-13 15:54:26
Alerts play a critical role in the attack detection and response phases of security operations. The Alert management function focuses on security detection scenarios and provides centralized management of security-related alert rules and their triggered history events.
Through this feature, users can flexibly adapt to security monitoring requirements: they can either directly enable pre-defined rules established by the security operations team for various attack scenarios or define custom alert strategies to achieve real-time awareness of abnormal business status. Users can also view alert history to understand and review previous attack events.
How It Works
System-Defined Rules and Custom Rules
System-defined rules are created by security operation experts, ensuring continuous monitoring for all hostnames that have been accessed to security protection and record alert history. Users can choose whether to receive notifications, but cannot edit or delete rules. The three types of system-defined rules currently supported are as follows:
| Rule Type | Rule Name |
|---|---|
| Attack Awareness Notification | The Website is suffering from L4 DDoS attacks. |
| Emergency Response Notification | L7 DDoS attacks reduce website availability. |
| Service Switch Notification | The CPS IP is blackholed. |
System-defined rules cannot be edited or deleted.
Custom Rules allow users to define their own alert rules based on specific business requirements, covering scenarios such as network-layer protection, application-layer protection, and resource route switching. Users can freely configure multidimensional detection strategies according to different monitoring objectives and customize flexible notification methods to meet operational needs.
Alert Cycle
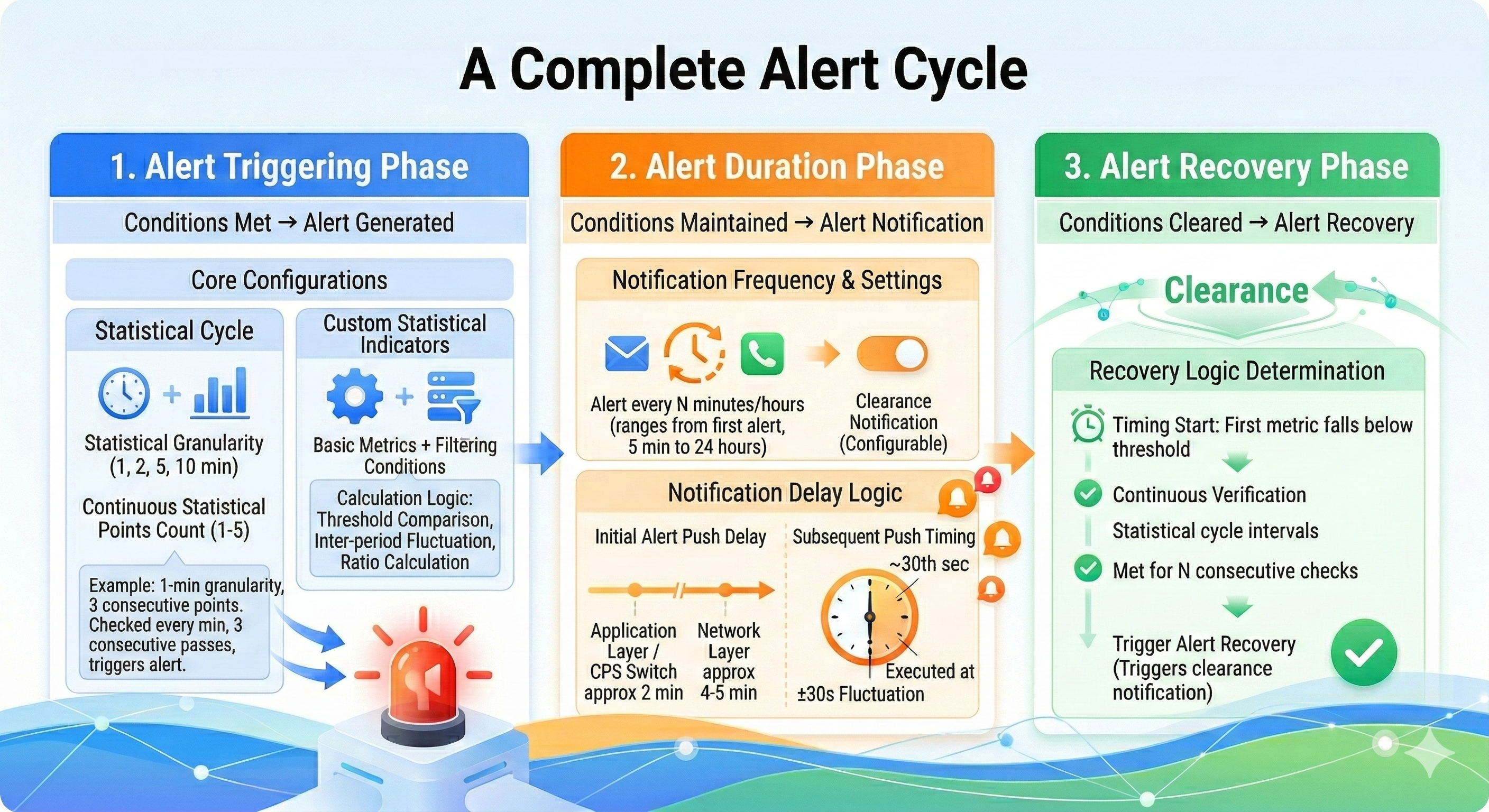
A complete alert lifecycle consists of the following three stages:
- Alert Triggering Phase: Alert occurs when conditions are met.
- Alert Duration Phase: Alert notifications are sent as the conditions remain met.
- Alert Recovery Phase: Alert is resolved after the conditions are no longer met.